Easily Manage Your Domain DNS – No Tech Skills Needed
Your domain’s DNS controls where your website, email, and every online service is pointed. With our DNS Manager, you get full control in a user-friendly dashboard—free with every domain. Whether you need to connect to a website builder, update email servers, or verify your site with Google, it’s all a few clicks away.
- Update All DNS Records: Manage A, CNAME, TXT, SPF, and MX records for full flexibility.
- Easy-to-Use Interface: Add, edit, or remove records instantly—no complicated menus.
- Instant Propagation: Most updates take effect in minutes, with a clear “zone valid” indicator.
- Free With Every Domain: No hidden fees or upcharges for DNS control.
- Connect Anywhere: Use your domain with Google, Wix, Shopify, Squarespace, Microsoft 365, and more.
- Reset in One Click: If you ever get stuck, restore default settings in seconds.
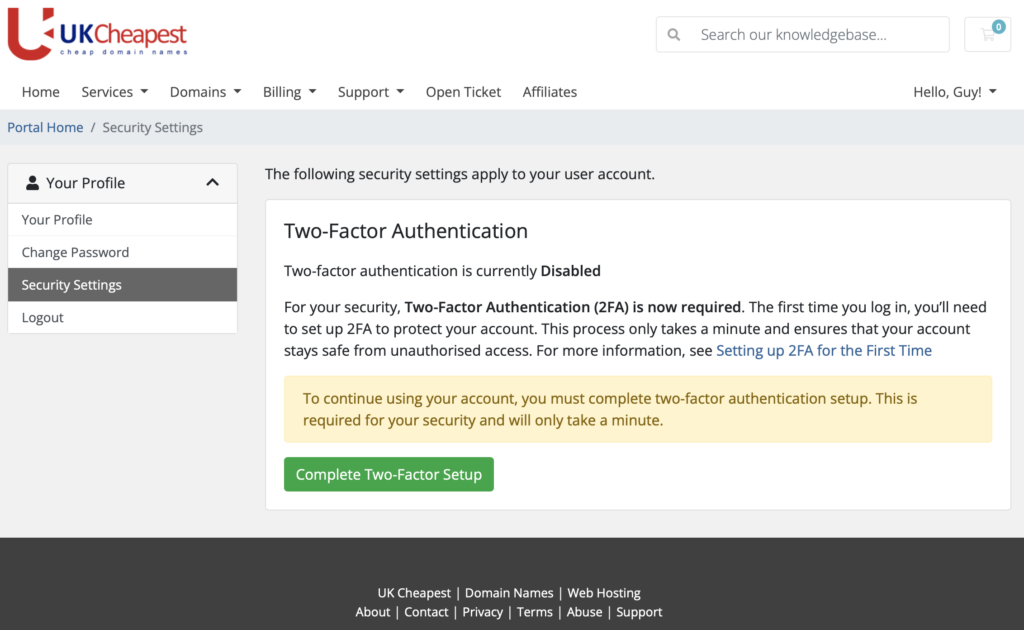
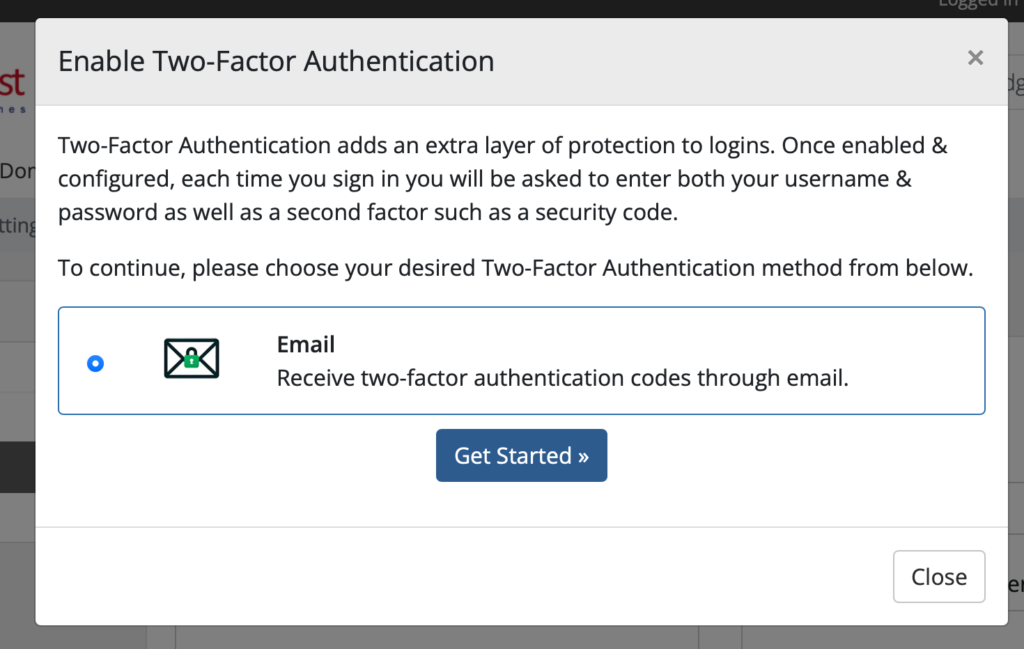
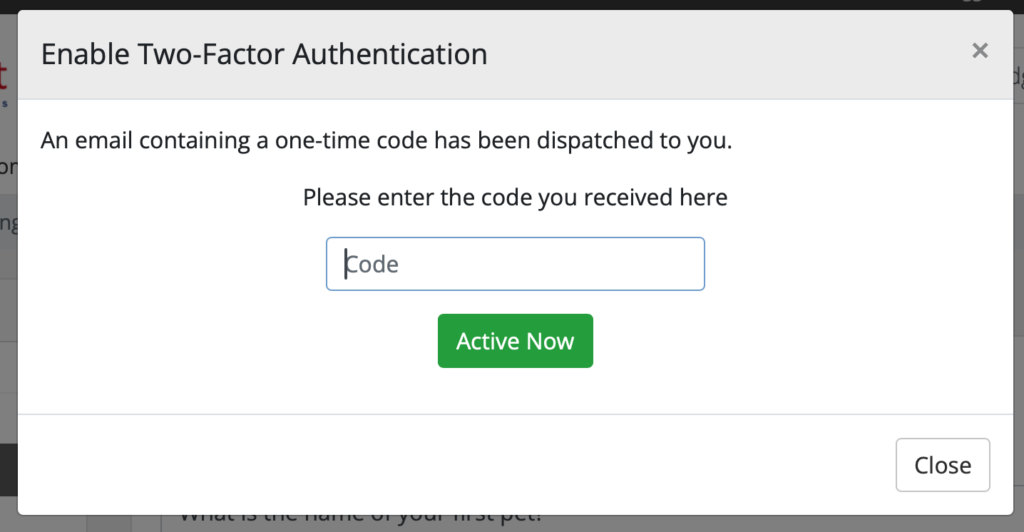
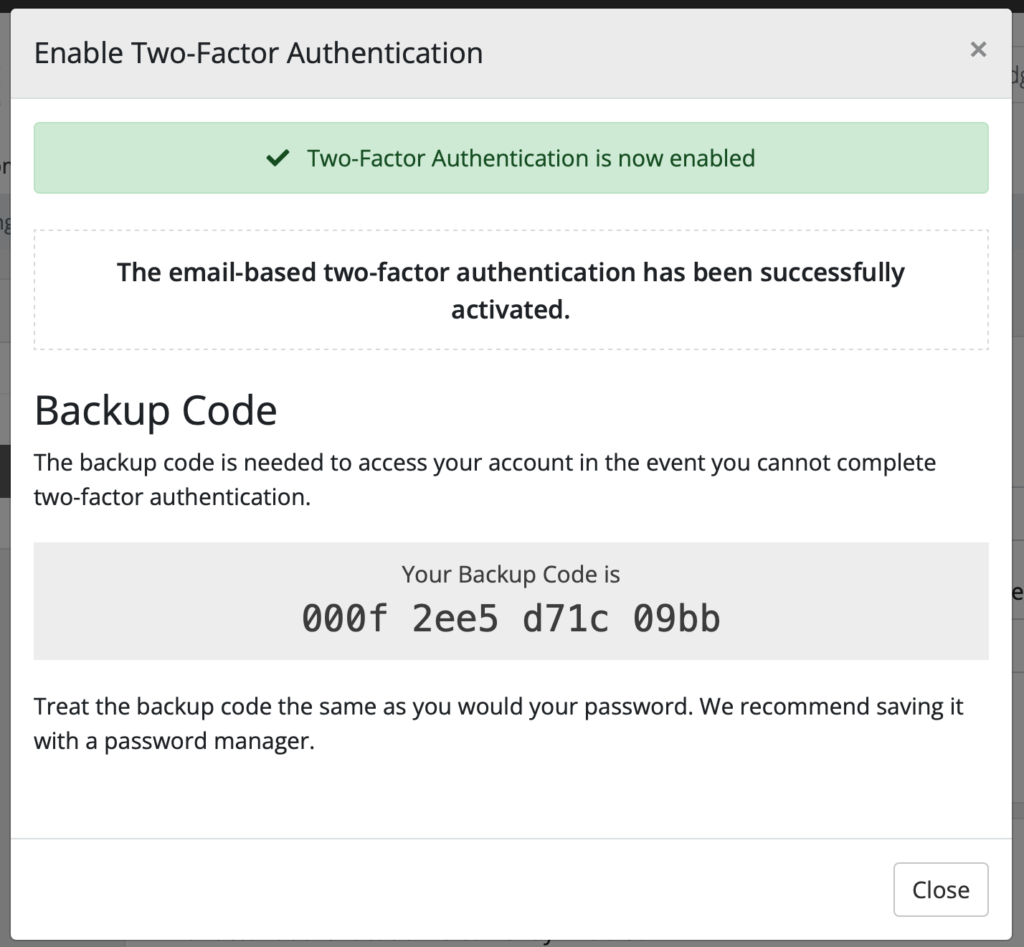
How It Works
- Log in to your UKC account and select your domain.
- Open DNS Manager from your control panel.
- View and Edit Records:
- A Record: Points your domain to a website (IP address)
- CNAME: For subdomains (like www) pointing elsewhere
- MX Records: Route email to your mail provider
- TXT/SPF: Used for verification, security, or third-party services
- Make Changes Instantly:Add new records or update existing ones. Changes are saved with the blue “Apply” button.
- See Status At A Glance:If your DNS is set up correctly, you’ll see a green “This zone file is valid” message.
- Easy Recovery:If something goes wrong, use “Reset to Original Defaults” to restore standard settings.
Interface Preview
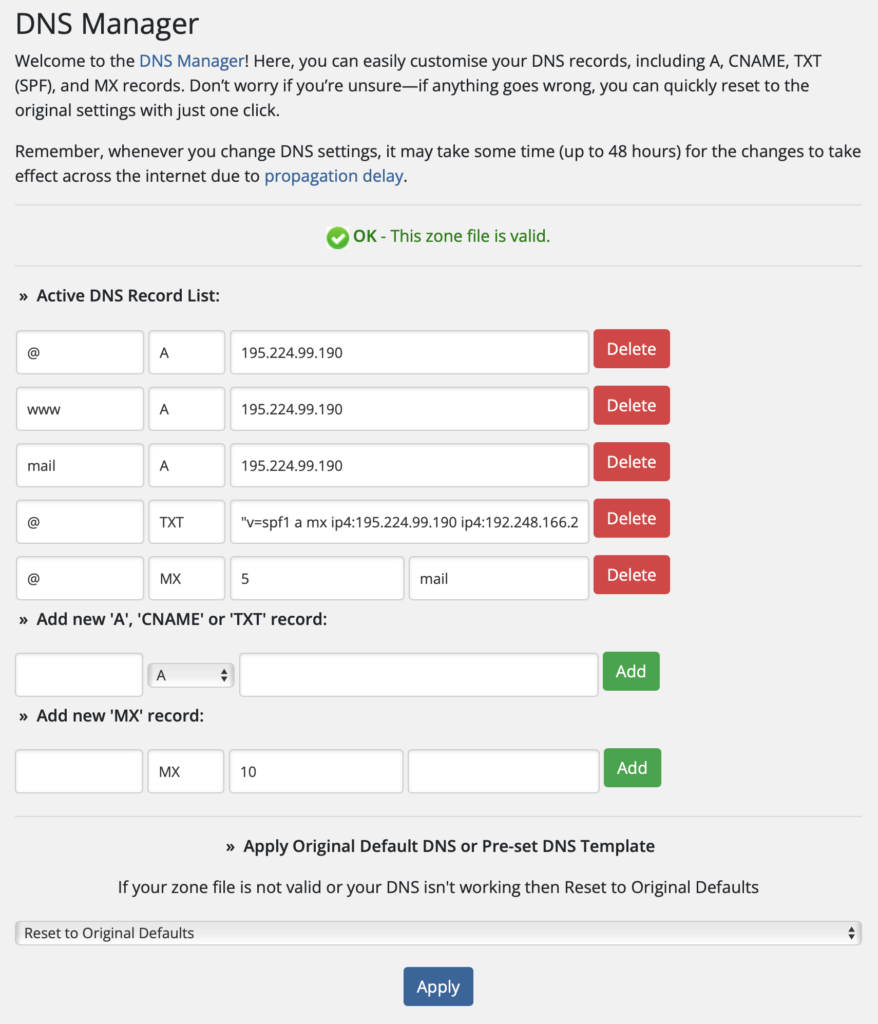
Our DNS Manager puts you in control: add, edit, or remove DNS records in seconds. Everything is labelled clearly, with instant feedback on your changes.
Frequently Asked Questions
How long do DNS changes take to go live?
Most DNS changes are instant, but some may take up to 48 hours to propagate globally.
Can I break my website by changing DNS?
Only if you point your domain to the wrong place. If unsure, you can always reset to default settings.
Is the DNS Manager really free?
Yes! Full DNS control is included with every domain registration at UK Cheapest.
Can I use my domain with third-party services?
Absolutely! Our DNS Manager is compatible with all major website builders, email hosts, and verification services.
Get Started Today
Ready to take control of your domain?
Log in to your UKC account and try out our DNS Manager now. Need help? Contact our UK-based support team – we’re here 24/7.
Tip:
If you’re moving to Google, Wix, Squarespace, Microsoft 365, or any service, check their help page for DNS records—they’ll give you the exact details to enter here!
Still have questions?
Reach out to us – our friendly support team is always happy to help you get your domain working perfectly.