At UK Cheapest, we take data protection seriously. As a hosting provider, we act as a Processor under UK GDPR, with our customers being the Controllers of their own data. This page provides the key information you need for your Data Protection Impact Assessments (DPIAs) and compliance documentation.
1. Data Processing Addendum (DPA)
We provide a standard Data Processing Addendum (DPA) which sets out our respective roles and responsibilities:
- You are the Controller
- We are the Processor
2. Data Location & Storage
Customer production data is stored and processed only within secure data centres located in the United Kingdom and European Union.
- Primary infrastructure partners include EUKhost Ltd (UK), Contabo GmbH (operating UK data centres), Vultr (UK/EU regions), and a local UK-based data centre provider under direct contract with UKC.
- No customer production data is stored outside the UK or EU.
- Where service providers are headquartered outside the UK/EU (e.g. Vultr, Cloudflare, Google), transfers are governed by approved safeguards such as the UK International Data Transfer Agreement (IDTA) and EU Standard Contractual Clauses (SCCs).
This ensures that your data remains protected in compliance with UK GDPR and EU GDPR requirements.
For formal documentation, UK Cheapest provides a Data Processing Addendum (DPA) that sets out Controller/Processor roles and responsibilities under GDPR -> Download the GDPR Processing Addendum (PDF)
3. Sub-processors
In addition to the above hosting partners, we rely on carefully selected sub-processors to deliver services:
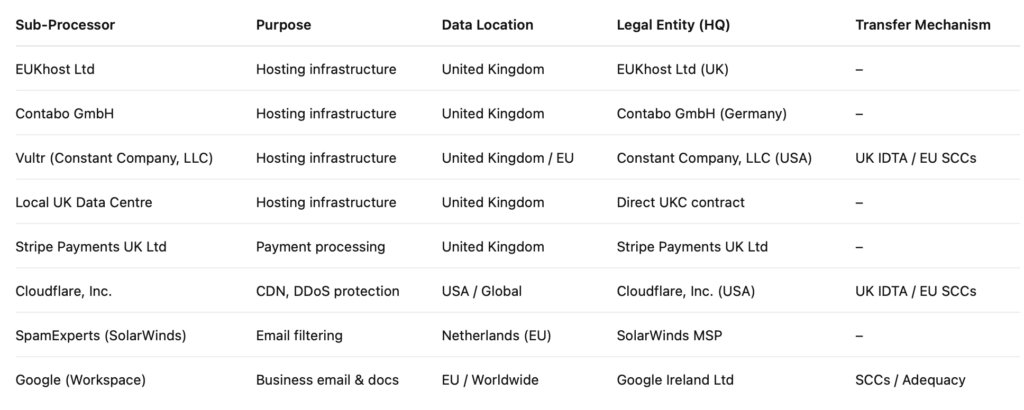
Notification of changes: We will update this list here on this page at least 30 days before engaging any new sub-processor.
4. Security Standards
We implement strong technical and organisational measures in line with industry best practices, including:
- Encryption in transit (TLS/SSL) and at rest
- Strict access control and authentication
- Regular patching and security monitoring
- Firewall and intrusion detection systems
- Data backups with secure off-site storage
While UK Cheapest is not ISO 27001 certified, our security measures are designed in accordance with ISO 27001 standards.
5. Breach Notification
In the unlikely event of a personal data breach, UK Cheapest will notify affected Controllers without undue delay, providing sufficient details to assist with your own regulatory obligations and customer communications.
6. Contact
For all GDPR, privacy, or compliance-related queries:
Email: gdpr@uk-cheapest.co.uk
Last updated: September 2025 (Vultr and Cloudflare added to sub-processor list)


 Like most websites, this one uses cookies.
Like most websites, this one uses cookies.
 Servers within our data centres are fed power through an Uninterrupted Power Supply (UPS) that takes raw power from a utility to control, modulate, and supply it to thousands of individual servers.
Servers within our data centres are fed power through an Uninterrupted Power Supply (UPS) that takes raw power from a utility to control, modulate, and supply it to thousands of individual servers.